Trezor Review Introduction

Trezor was the world’s first bitcoin hardware wallet that stores and protects your bitcoins and other cryptocurrencies. It is a small computer device that connects to your laptop with a USB cable. Your cryptocurrency and all private keys are encrypted and stored offline on the device. In that way, Trezor is an isolated environment, and you use its small display to verify transactions. This means you can safely use the hardware wallet even if your computer has malicious software. A hardware wallet is the safest way to protect your bitcoin and cryptocurrency.
Trezor is the gold standard for hardware wallets in the crypto market. The product is manufactured by a well established and trusted company. The Trezor hardware wallet has not only the highest security but also a good user experience. It combines security from a paper wallet along with the convenience of an online wallet. The user gets the best of both worlds, and it has caused Trezor to explode in popularity recent years.
A hardware wallet that protects your private keys offline is the safest way to store your bitcoin and cryptocurrencies. We recommend everyone to buy a hardware wallet to protect their digital money. To learn more about hardware wallets, read our Bitcoin Wallet Guide. In this review, you will learn everything about the Trezor hardware wallet.
How does it work?
You should never store bitcoin at an exchange because it’s not safe. Hardware wallets protect your private keys (which verify ownership of bitcoin) against online and offline risks. Trezor is very easy to use with clear instructions when connecting it to your computer. There are only two buttons used to confirm or deny a transaction. Under the section “Wallet Security”, we will explain in detail how the Trezor hardware wallet works and protects your cryptocurrencies.
When you first connect your Trezor, you will receive a recovery password if your device should break or disappear. You can feel confident that your bitcoin and cryptocurrency are safe even if you lose your Trezor. We will explain in detail how this works in the “Backup and Recovery” and “Setup and Installation” sections later in the review.
Hardware wallet privacy
Trezor offers excellent privacy, and users can be completely anonymous. The manufacturer is unable to track your actions after you have received the device because it has no serial number. You don’t need a username or password when you purchase a Trezor hardware wallet, and all software is open source. The confidentiality of your transactions depends on which software you use with your wallet.
The company offers its own web-based software at wallet.trezor.io but there are also other applications that work with your Trezor. To name a few, you can use Electrum, GreenAddress and MultiBit HD on your laptop or GreenBits and Mycelium if you’re using Android.
There is a risk that information will be leaked while installing your Trezor with their web wallet. To ensure your anonymity, you can use their Chrome extension or Python tool and configure the device on an offline computer.
Order and delivery
You can order a Trezor hardware wallet on their website. Either you can order a Trezor for €89 or order their Multipack and save €22 when buying three units (1x black, 1x white and 1x random color). For security reasons, DO NOT order a hardware wallets from eBay or other retailers.
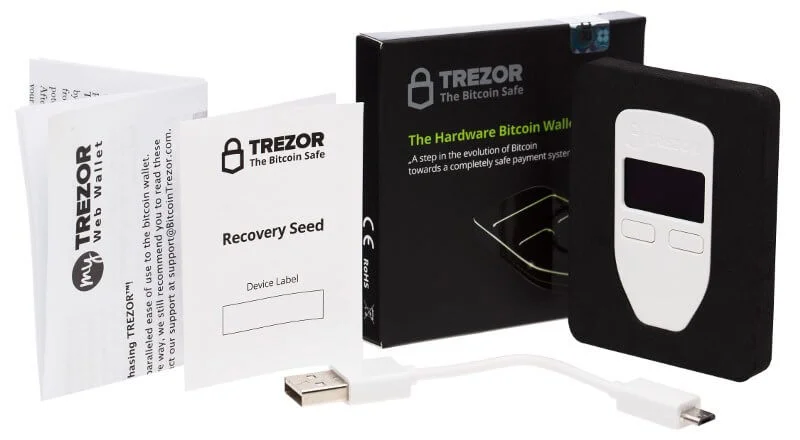
When your Trezor is delivered, check that the device is unused. The package should be wrapped with plastic, have security tape, and glued together firmly. If the package has been opened or the security tape has been removed, you need to replace the device with a new hardware wallet. If the package is sealed, don’t worry. In the box, you get a Trezor device, USB to micro USB cable, small cord, and user manual.
The hardware wallet is shipped from the Czech Republic and delivery time varies depending on region and supply. Trezor is the most reliable hardware wallet on the crypto market. This may result in demand exceeding the supply during certain periods, affecting delivery time.
Buy Trezor Hardware Wallet for $99

Trezor Background
SatoshiLabs is the company behind the hardware wallet and was founded in 2013 with its headquarters in Prague, Czech Republic. The company started working with Slush Pool, which was first on the market with a bitcoin mining pool. Then in August 2014, Trezor was launched as the world’s first bitcoin hardware wallet.
Trezor has consistently been manufactured for many years and the company has gained high reliability. Trezor is considered to be the most reliable crypto hardware wallet because it has a strong brand and well-known manufacturer. SatoshiLabs is transparent with the manufacturing and software that helps users to protect their bitcoin and cryptocurrencies.
It’s open-source and all technical decisions are discussed in their community of developers. Software development is also reviewed by independent third parties, ensuring that there is no loophole. Trezor is still one of the most popular hardware wallets on the crypto market. This is with the help of the developer community that continuously improves the Trezor device.
The company has more than 20 employees, including developers, customer service, bitcoin and security experts, and more. The name of the hardware wallet “trezor” is translated to “vault” in the Czech Republic and most Slavic languages. The Trezor hardware wallet is a vault for Bitcoin hodlers.
Below you can read about the company’s values from their website:
We are ambitious pioneers of technology, who strive to bring cryptography to the masses! Innovation is our engine; never-ending research and development keeps us at the top. Our aim is to understand and deliver secure yet easy-to-use solutions to real problems. We create and foster our open-source cryptography environment, the “TREZOR ecosystem,” for which we continuously develop flagship applications.
User Experience & Features

User Experience
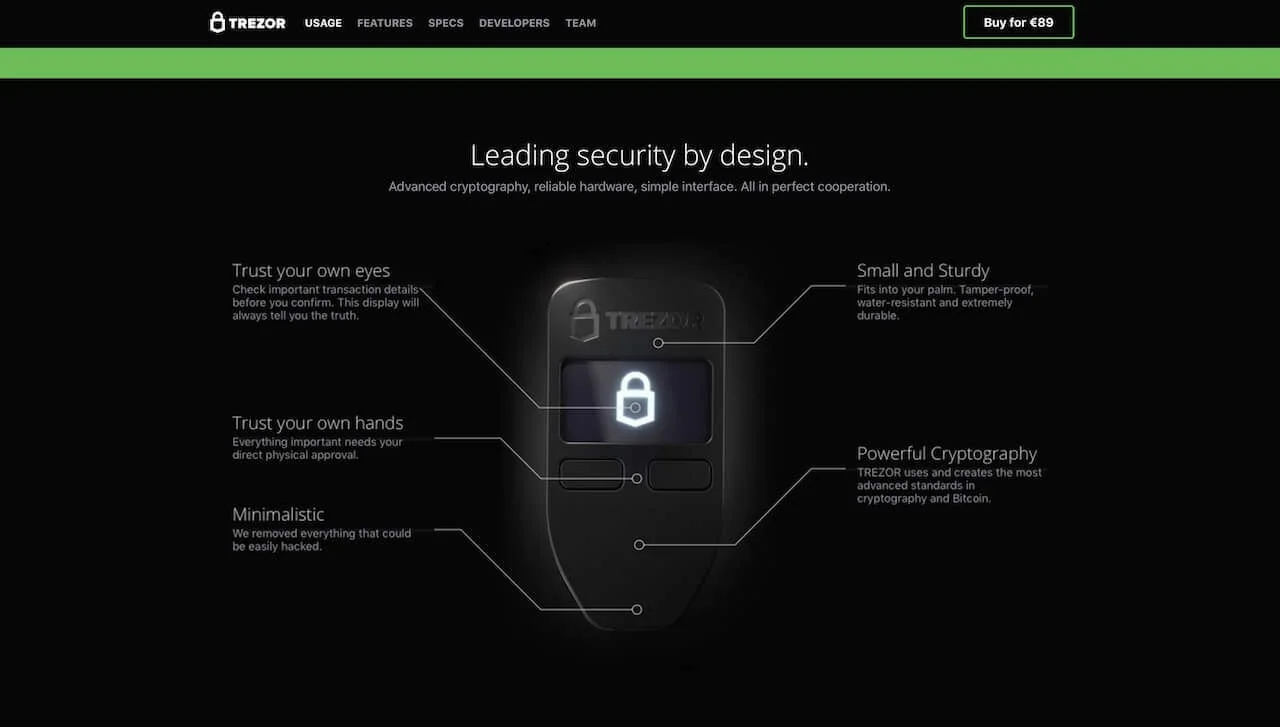
Trezor is a hardware wallet with a simple but secure design and interface. Let’s start with the hardware. The device is made of plastic and has an OLED screen, two buttons and a micro USB jack on the bottom. When Trezor was launched, they manufactured it in metal to the first customers. That is unfortunately no longer available. The device is not waterproof, but the manufacturer says it is at least water resistant. The screen size is 128×64 pixels, which is enough to present all information to verify a transaction.
When using your Trezor, plug it into your computer or mobile phone with the micro USB cord. You only need to connect Trezor when you want to send cryptocurrency. You can always receive money without connecting the device. It’s effortless to use the hardware wallet because it automatically starts and turns off when connected. At the end of the review, we will help you get started with your Trezor hardware wallet.
If you have installed your Trezor, you have a PIN code that you use to verify transactions. When you enter your PIN, the numbers are randomly displayed on your Trezor and never on your computer screen. In other words, even if your computer is exposed to malicious code or monitored, they will not be able to access your password. Your PIN is encrypted and only visible on your Trezor wallet. This makes the hardware wallet very secure and to verify transactions is quick and straightforward.
The user experience is good, but of course, varies depending on which software you use with your Trezor. If you want to buy smaller cryptocurrencies, you may need to use external software which can have a worse user experience. You can read more about using different cryptocurrencies under the “Cryptocurrency Support” section.
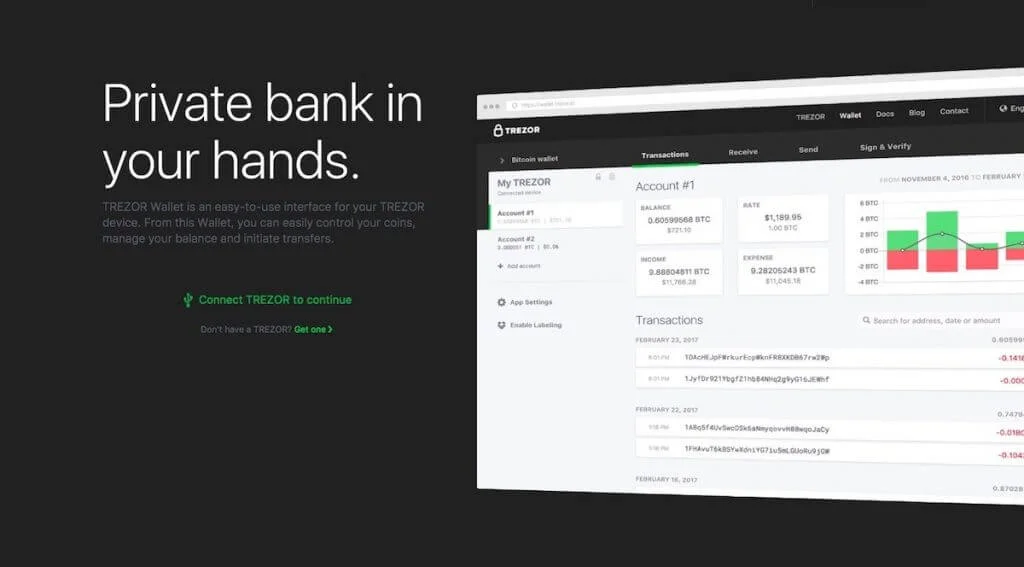
When you log in to their own web-based software, you get a good overview of your addresses and transactions. You can generate an endless number of addresses and the interface is clear for sending, receiving, signing and verifying transactions.

Trezor Features
Trezor has many different features and integration with third-party wallets and services. Because Trezor is open source, other companies can integrate their services with the hardware wallet. MyEtherWallet is a company that works with Trezor to protect your Ether on the hardware wallet.
There are exchanges, such as Bitstamp, where you can connect your Trezor for direct transfers. You can also connect your Trezor with platforms, such as WordPress, for secure login. The hardware wallet receives new features and integration with more services every year. Below we have listed a selection of features available:
- Wallet for cryptocurrency: In addition to Bitcoin, you can protect digital currencies such as Ethereum, Litecoin, Dash, and Zcash.
- Third party integration: Trezor can be linked to other platforms for direct transfer, secure login, and more.
- Password manager: Can be used with your Trezor to encrypt passwords and sync them with your cloud services.
- Two-factor authentication (2FA): Creates additional protection for your accounts and your Trezor can be used as a security token.
- Admin SSH access: Enables a secure connection that protects access to your server and data. Works with one or more sessions.
- Login without password: With Trezor Connect, you can log in securely with the press of a button instead of your password.
- Sign and encrypt with GPG: Trezor protects your data by encrypting all documents and emails you create with GPG.
- Sign and verify messages: It’s easy to sign messages and documents to verify your ownership.
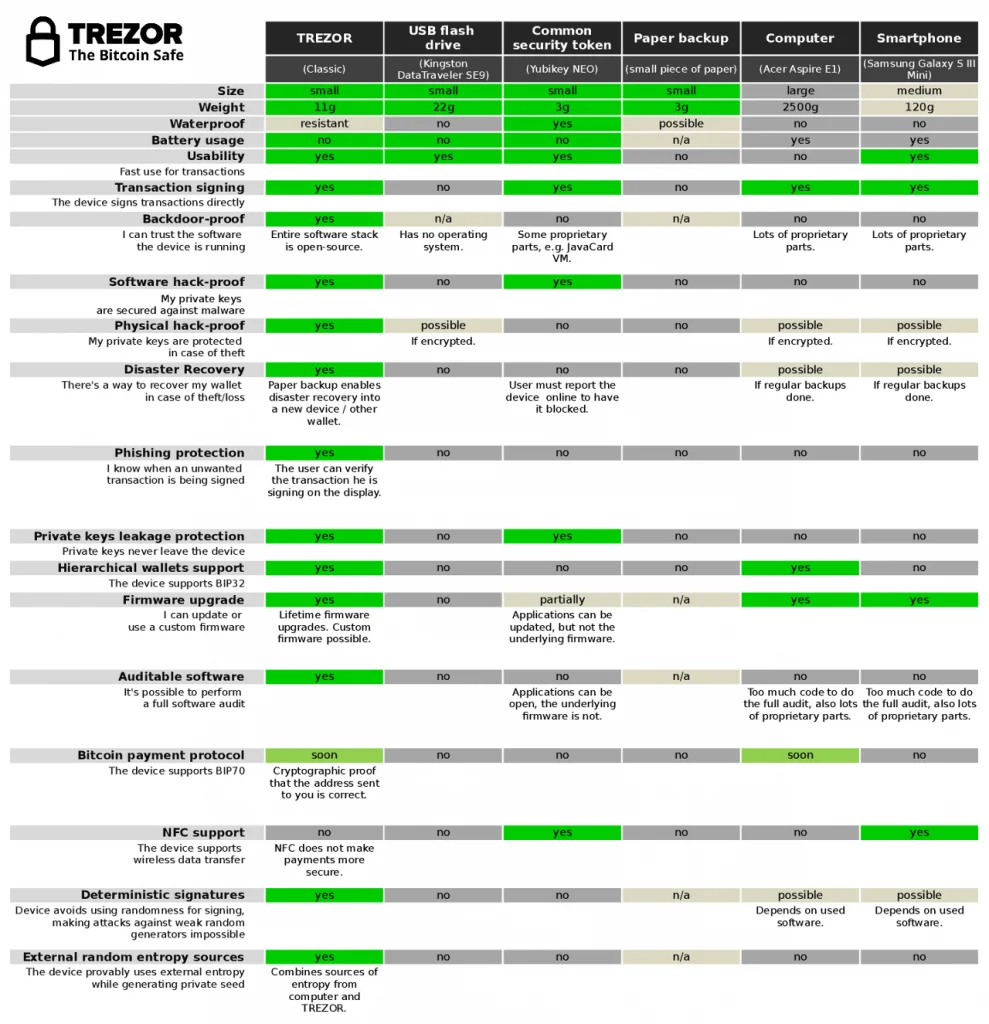
Wallet Security
The crypto market is particularly vulnerable to hacker attacks making a hardware wallet necessary. Trezor protects your bitcoin private keys and cryptocurrencies with encryption on an offline device. There are many different safety benefits to using a Trezor hardware wallet instead of an online wallet.
There are several layers of security measures that protect your money against both physical and virtual theft. In the next section, we will explain how to back up and perform recovery of the hardware wallet. Here we explain how Trezor works and protects your cryptocurrency.
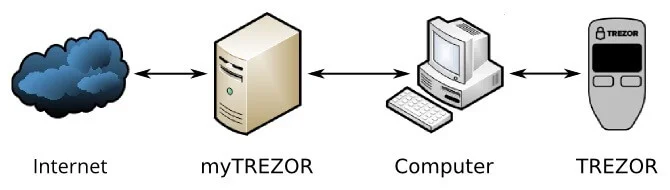
How does Trezor work?
When you install your Trezor, you get to choose a PIN that you use to confirm transactions. The PIN is used with two buttons on the hardware wallet to confirm or deny transfers. When you enter your PIN, the numbers are randomly displayed on your Trezor and never on your computer screen.
A software is needed to interact with Trezor. To initiate a transaction, you enter an amount and address for the program. After that, the program communicates with Trezor and sends the unsigned transaction. Trezor displays the information on its screen and asks you to sign the transaction by entering your PIN. If you approve the transfer, Trezor will notify it to the program that then sends out the transaction to the network.
Your bitcoin is secure because private keys never leave the hardware wallet. Even if the software you are using is being hacked, your cryptocurrencies are secure on your Trezor.
How are your cryptocurrency protected?
Trezor protects you from a variety of hacker attacks. Everything from a simple keylogger to remote control of your computer. A hacker needs both your PIN and your Trezor to complete a transaction. It’s not enough for the hacker to know your code because the numbers are visible only on the hardware wallet screen.
All of your private keys are stored on your Trezor, and the user either needs the PIN together with the hardware wallet or recovery seed to access the cryptocurrency.
Backup and Recovery

When you install your Trezor, you get a recovery seed that serves as a backup of your hardware wallet. At the end of this review, we will help you to install and activate your Trezor. Below we will explain how the backup works and talk about advanced security settings.
Backup of Trezor
If your Trezor is stolen or lost, you can restore your cryptocurrency with your recovery password on another Trezor. Backing up your hardware wallet is easy. When you activate your Trezor, you get 24 words that will be your recovery password. This password is generated offline, and only appears on the hardware wallet screen during installation.
In the package, you get a recovery card that you can use to write down and save the password. You can also secure your backup by purchasing a physical wallet in metal to store your recovery password. For example, Cryptosteel protects your password from water, fire, and other destruction.
Advanced security settings
For extra security, you can choose a passphrase encrypted seed for your 24-word password. This means that your recovery password consists of 25 words. However, if you forget the passphrase you can’t restore your Trezor.
Another safeguard measure is the ability to create a hidden wallet. In that case, you use multi-passphrase encryption to generate hidden wallets. This can protect the user from being threatened to tell their password. Such an attack is usually called the $5 wrench attack by security experts.
Cryptocurrency Support

Trezor’s hardware wallet currently supports Bitcoin, Ethereum (with all ERC-20 Tokens), Litecoin, Bitcoin Cash, Ethereum Classic, Zcash, Dash, Namecoin, Dogecoin and Bitcoin Testnet. Integration with Trezor is continuously expanded and improved by developers. As mentioned above, they use open source code. Therefore, we have different types of wallet software. This also means that the interface differs between the various Trezor wallets.
Although the interface may be different for cryptocurrencies, everyone is as secure on your Trezor hardware wallet. Below we have listed all the cryptocurrencies and the primary software that works together with Trezor. In the next section, you can view all wallets and their features. Trezor Wallet, which is their own software, is very easy to use. MyEtherWallet which is popular with Ethereum also works well. We have not tested any other software available.
| Wallet interfaces with cryptocurrencies for Trezor | |
|---|---|
| Bitcoin | Trezor Wallet |
| Litecoin | Trezor Wallet |
| DASH | Trezor Wallet |
| Zcash | Trezor Wallet |
| Bitcoin Cash / Bcash | Trezor Beta Wallet |
| Ethereum | MyEtherWallet |
| Ethereum Classic | MyEtherWallet |
| ERC-20 Tokens | MyEtherWallet |
| Namecoin | None |
| Dogecoin | None |
| Bitcoin Testnet | Custom Trezor Wallet |
Developer Community
Trezor has a large community of developers that improves and creates new software for the hardware wallet. There are especially many wallets that connect with Trezor to store and protect cryptocurrencies. The user experience varies, but the security is the same. Your private keys will remain encrypted on your hardware wallet regardless of which wallet you use together with Trezor.
This means your Trezor hardware wallet is secure even if the software is hacked. The security can not be questioned. The company also has a good team of developer and customer service. Trezor proved this when Bitcoin’s blockchain was forked, and Bitcoin Cash / Bcash was created.
However, complaints arose because the software update needed to support Bcash was delayed. According to us, the company performed well under the circumstances and the customers were treated fairly. Trezor could as well have said that their hardware wallet doesn’t support Bcash. The Trezor hardware wallet works with Windows, MacOS and Linux. Below are listed wallets and their compatible user features:
| Wallet : | : | : | : | : | : | : | : | : | : | : |
|---|---|---|---|---|---|---|---|---|---|---|
| ArcBit | ✓ | ✓ | ||||||||
| Blockonomics | ✓ | ✓ | ||||||||
| Copay | ✓ | ✓ | ✓ | ✓ | ✓ | |||||
| Chrome Extension | ✓ | ✓ | ✓ | ✓ | ✓ | |||||
| Electrum | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ||||
| Electrum-DASH | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ||||
| Electrum-LTC | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ||||
| Etherwall | ✓ | ✓ | ✓ | |||||||
| Mycelium | ✓ | ✓ | ✓ | ✓ | ||||||
| TREZOR Wallet | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | |
| Sentinel | ✓ | ✓ |
| Basic Setup | Safe Recovery | Personal wallets | Shared wallets | Hidden Wallets With Passphrase | Watch-only mode | Show on TREZOR | Update Firmware | Wipe device |
Setup and Installation
Installing and activating Trezor is easy, and it shouldn’t take longer than 10-15 minutes. There are three different ways to install your Trezor; Visit their web-based wallet, download their TREZOR Chrome Extension or install via the terminal on your computer.
Most users activate Trezor on their website because it’s the easiest option. The advantage of their Chrome Extension is that you can install the hardware wallet offline. This is recommended because it is better for your privacy. If you choose to activate it on their website, you will download a “bridge” when you connect your hardware wallet. Your computer needs it to communicate with Trezor. If you want to learn more, read their user manual.
Then it’s easy to follow the instructions and select the PIN code, device name, and a recovery password. When done, you can disconnect your Trezor. You don’t need to do anything on your computer.
Get started with Trezor
Step 1: On the package, your Trezor comes in, you will be asked to visit trezor.io/start. They will first show how to create a PIN and how it works with your hardware wallet. Above in the “Wallet Security” section, we have a detailed description of how your Trezor and PIN code works. Trezor also has a good video guide that shows how to use your PIN:
Step 2: The next step is about your recovery seed. It’s important to understand how it works if your Trezor is stolen or lost. Above in the “Backup and Recovery” section, we have a detailed description of everything you need to know. Below is a quote from their website:
Never make a digital copy of your recovery seed and never upload it online. Keep your recovery seed in a safe place. TREZOR cannot be held liable for financial losses incurred through the client’s improper care of sensitive information.
Step 3: Lastly you are advised to subscribe to their newsletter. You will receive emails about important updates of your Trezor hardware wallet. It’s a good idea to stay up to date because the crypto market is always evolving. Here you can subscribe to their newsletter.
Summary and Conclusion
Trezor was launched by SatoshiLabs in 2014 and became the world’s first bitcoin hardware wallet. The company has built a big and trustworthy brand in the crypto market. For this reason, many people mean that Trezor is the safest hardware wallet you can buy.
The company uses open source software which is reviewed by independent third parties. The Trezor has a simple but secure design and interface. The wallet is easy to use with two buttons on the front to confirm or deny transactions. The user experience is good, but will of course vary depending on the software.
The hardware wallet currently supports Bitcoin, Ethereum (with all ERC-20 Tokens), Litecoin, Bitcoin Cash, Ethereum Classic, Zcash, Dash, Namecoin, Dogecoin and Bitcoin Testnet. In addition to storing and protecting your cryptocurrencies, there are more user features. Including third party integration, password manager, two-factor authentication (2FA), admin SSH access, log in without password and more.
Your digital currencies are protected against a variety of different hacker attacks with Trezor. Everything from a simple keylogger to remote control of your computer. It’s not enough for the hacker to know your password because the numbers are visible only on the hardware wallet screen. Your bitcoin and cryptocurrency are safe even if your Trezor is stolen or lost. When you activate the wallet, you get a recovery seed password that will be your backup.
Trezor has a large developer community who continuously improves and creates new software for the hardware wallet. We believe Trezor will continue to be the leading hardware wallet on the crypto market.
Trezor conclusion
Trezor hardware wallet is a step in the development of Bitcoin towards an entirely secure payment system. You can store and protect your bitcoin without any intermediary or third party. Unlike other offline methods, you can perform secure transactions with Trezor without exposing your private keys to any computer.
It combines security from a paper wallet along with the convenience of an online wallet. Trezor is the ultimate solution for buying and selling bitcoin easily and safely. We strongly recommend purchasing a hardware wallet to protect your bitcoins or cryptocurrencies.
Subscribe to our newsletter below for updates. Get exclusive offers and the latest crypto news!
Trezor homepage screenshot 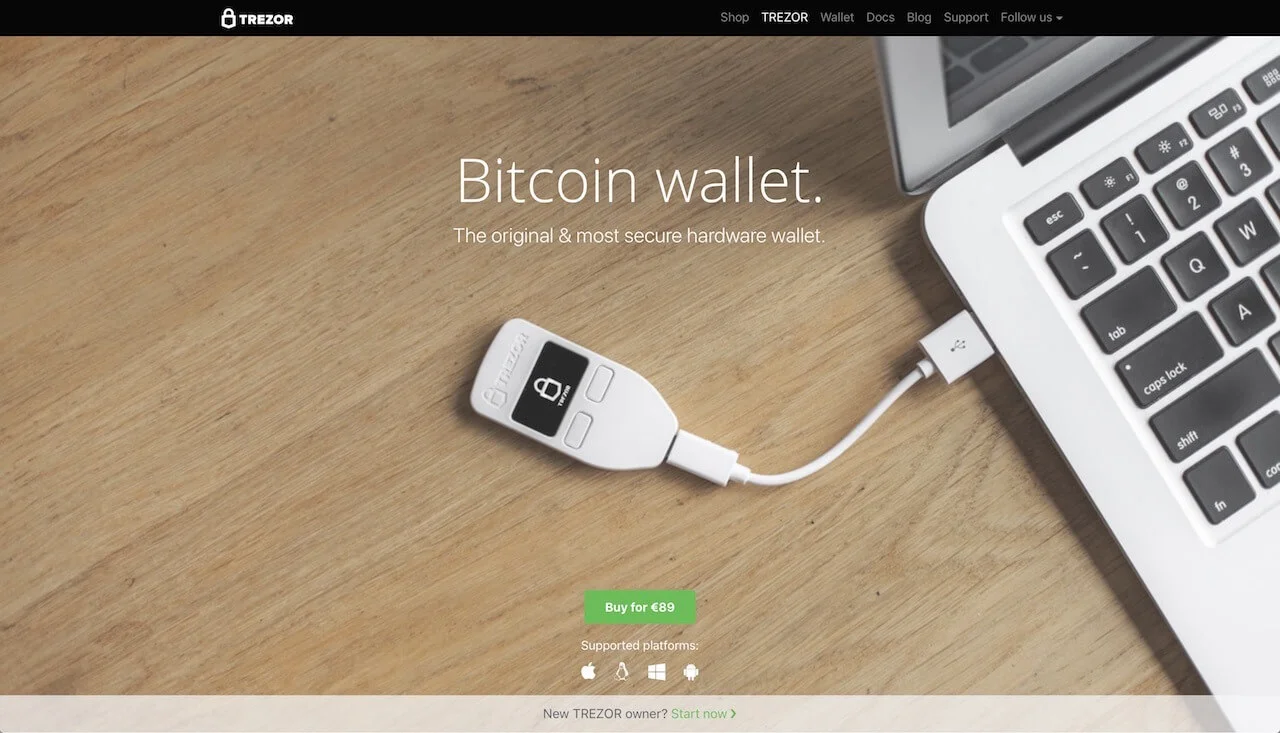 Trezor interface screenshot
Trezor interface screenshot 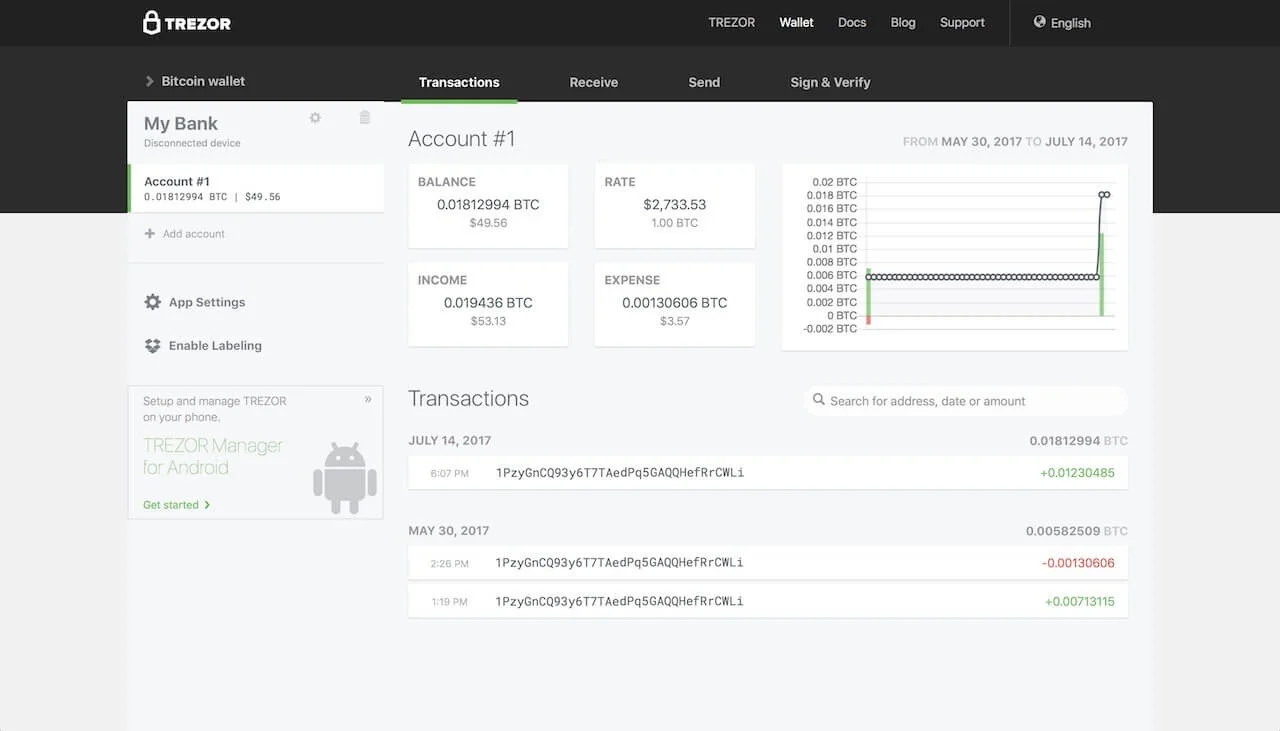 Trezor setup screenshot
Trezor setup screenshot 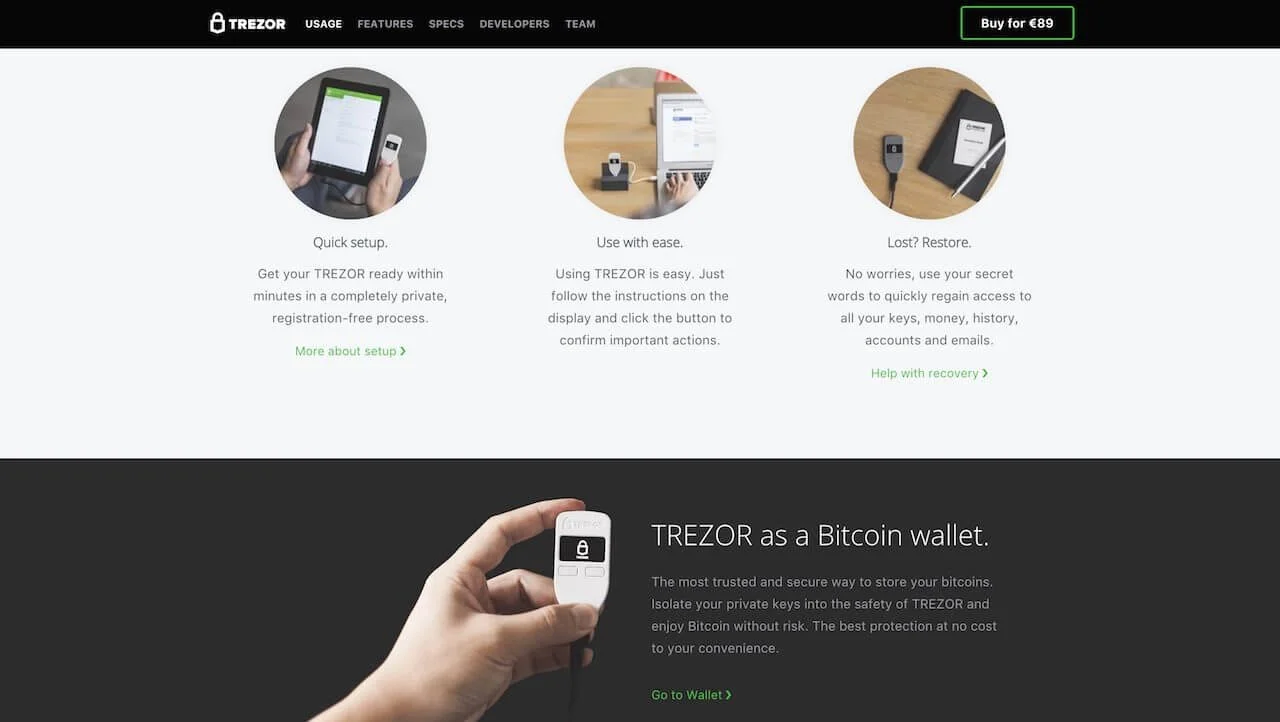 Trezor security screenshoot
Trezor security screenshoot